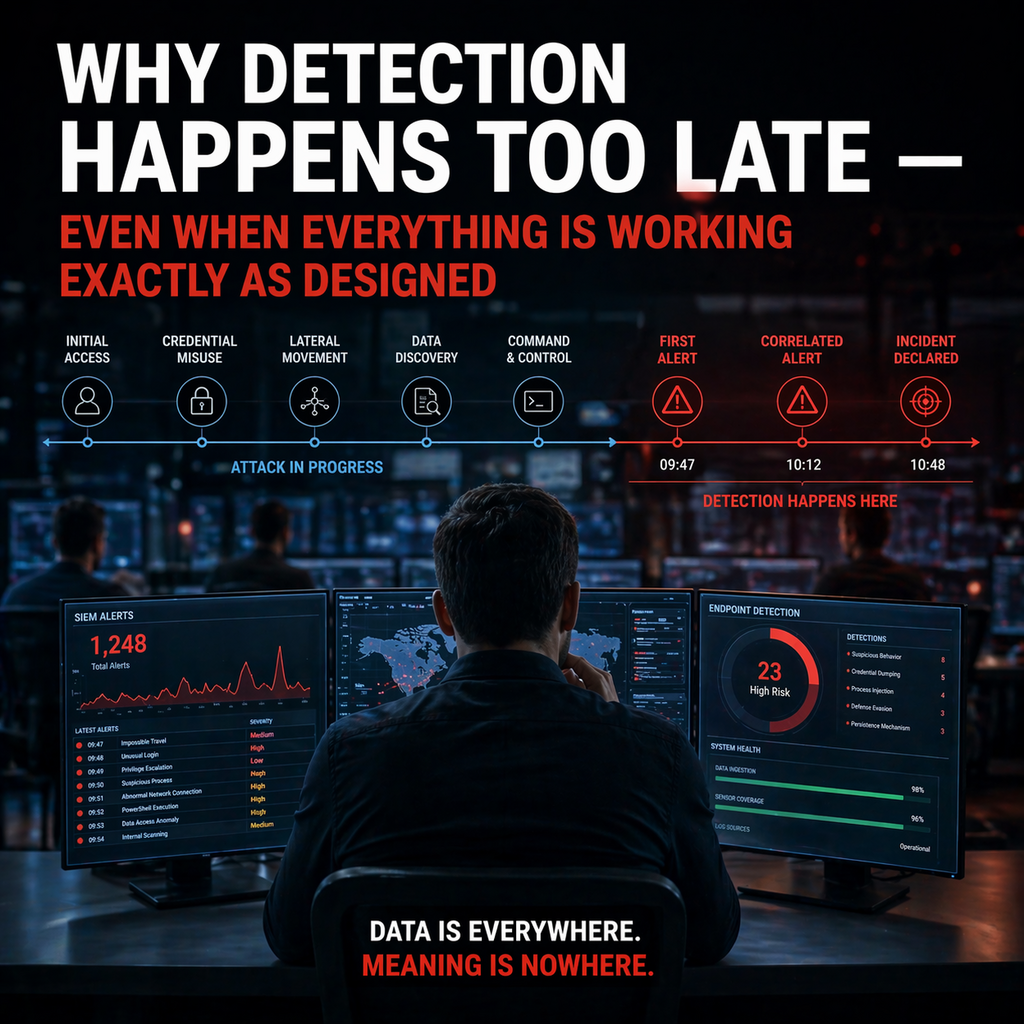
There are few areas in cybersecurity that create as strong an illusion of control as detection. On paper, everything works. Systems are running, data is being collected, alerts are being generated, dashboards are active. The infrastructure is in place, processes are defined, responsibilities are assigned. If you look at these elements individually, the conclusion seems obvious. Detection is implemented, detection is operational, detection is measurable. And yet, in real-world scenarios, a consistent pattern emerges. Attacks are detected, but too late. Signals are present, but their meaning is not understood in time. Systems function exactly as designed, but the outcome still falls short of expectations.This is where one of the least openly discussed weaknesses of modern security architectures begins to surface. Detection rarely fails because nothing is seen. It fails because what is seen is not understood in the right context. That distinction is critical, because it shifts the focus away from technology and toward the structure of the overall system.Externally, detection is often presented as a functioning and reliable layer of security. SIEM platforms process vast amounts of data, EDR and NDR systems continuously deliver telemetry, threat intelligence enhances visibility into potential risks. Alerts are generated in real time, correlations are performed, reports demonstrate activity. None of this is incorrect. But it is incomplete. It describes the existence of detection, not its effectiveness.Inside organizations, the reality is far more complex. Detection is not a single process. It is the result of multiple interconnected systems. Each system captures a piece of information, but none of them alone provides a complete picture. An unusual login is detected within an identity system. A slight behavioral deviation is observed by an endpoint tool. A minor anomaly appears in network traffic. Each of these signals is valid. Each is based on real data. Yet when viewed
Subscribe or
log in to read the rest of this content.
This article is part of Darkgate Feature Articles - Deep Access.
Strategic insight. Executive-level analysis.
Real infrastructure intelligence - beyond surface-level reporting.