From AI Assistant to Security Risk: The Hidden Challenges Inside Google’s Antigravity

What was designed as an innovative developer tool is quickly revealing a more complex and uncomfortable reality. With “Antigravity,” Google introduced a new generation of AI-powered coding environments aimed at increasing productivity, automating tasks, and assisting developers in writing and managing code. However, almost immediately after its release, security researchers began to highlight a critical […]
Your Photos Are No Longer Safe: SparkCat Malware Is Now Reading Your Screenshots to Steal Your Crypto

It’s a development many users completely underestimate – and that’s exactly what makes it so dangerous. While most people are still focused on not installing suspicious apps or avoiding typing their seed phrase into unknown platforms, the attack surface has already shifted. With the return of SparkCat malware, one thing becomes clear: even your photos […]
Data Breaches Are Back – And Nobody Is Talking About the Scale
From App Store Listing to $9.5 Million Theft: How a Fake Ledger App Drained Dozens of Crypto Wallets in Days

The next escalation level in crypto fraud has arrived – and it strikes at one of the most sensitive foundations of the digital ecosystem: trust in official platforms. What was long considered a secure distribution channel is increasingly becoming an attack surface itself. The recent case involving a fake Ledger app in Apple’s App Store […]
Trusted No More: How Fake Crypto Wallets Slipped Into Apple’s App Store and Turned Security Into an Illusion

The assumption that official app stores like Apple’s are inherently secure has long been one of the core pillars of modern digital trust. Especially in the sensitive world of finance and cryptocurrency, millions of users rely on the idea that apps listed there have passed at least a baseline level of security scrutiny. However, a […]
When “World-Class Encryption” Breaks: What the TeleGuard Case Really Reveals

The promises sound familiar – and for many users, reassuring: “world-class encryption,” “maximum privacy,” “no storage of sensitive data.” These are the kinds of claims modern messaging platforms use to position themselves against established players like Signal or Threema. But the recent case surrounding TeleGuard shows how quickly that trust can erode – and why […]
AI Doesn’t Need More Data – It Needs Your Behavior

We already looked at what Meta Platforms is doing internally, capturing mouse movements, clicks, keystrokes, and real user interactions inside the workplace to train AI systems that are no longer supposed to just respond, but to act. On the surface, this can be framed as another aggressive move in the race for AI dominance. Another […]
When Your Work Becomes Training Data: Inside Meta’s Silent Expansion of Human Behavior Capture for AI

At first glance, it looks like a logical next step in the evolution of artificial intelligence. Systems are no longer expected to simply process data. They are expected to understand how humans actually work. Not in theory, not through synthetic datasets, but in real operational environments. How people move through applications, how they click, how […]
You’re Monitoring Everything – But Understanding Nothing

It often begins with a sense of progress. Systems are expanded, new data sources are connected, additional dashboards are introduced. The environment grows, visibility increases, and with every new integration there is a growing belief that the organization is getting closer to reality. Logs from across the infrastructure are centralized, events are captured, correlations run […]
Why Detection Happens Too Late – Even When Everything Is Working Exactly as Designed
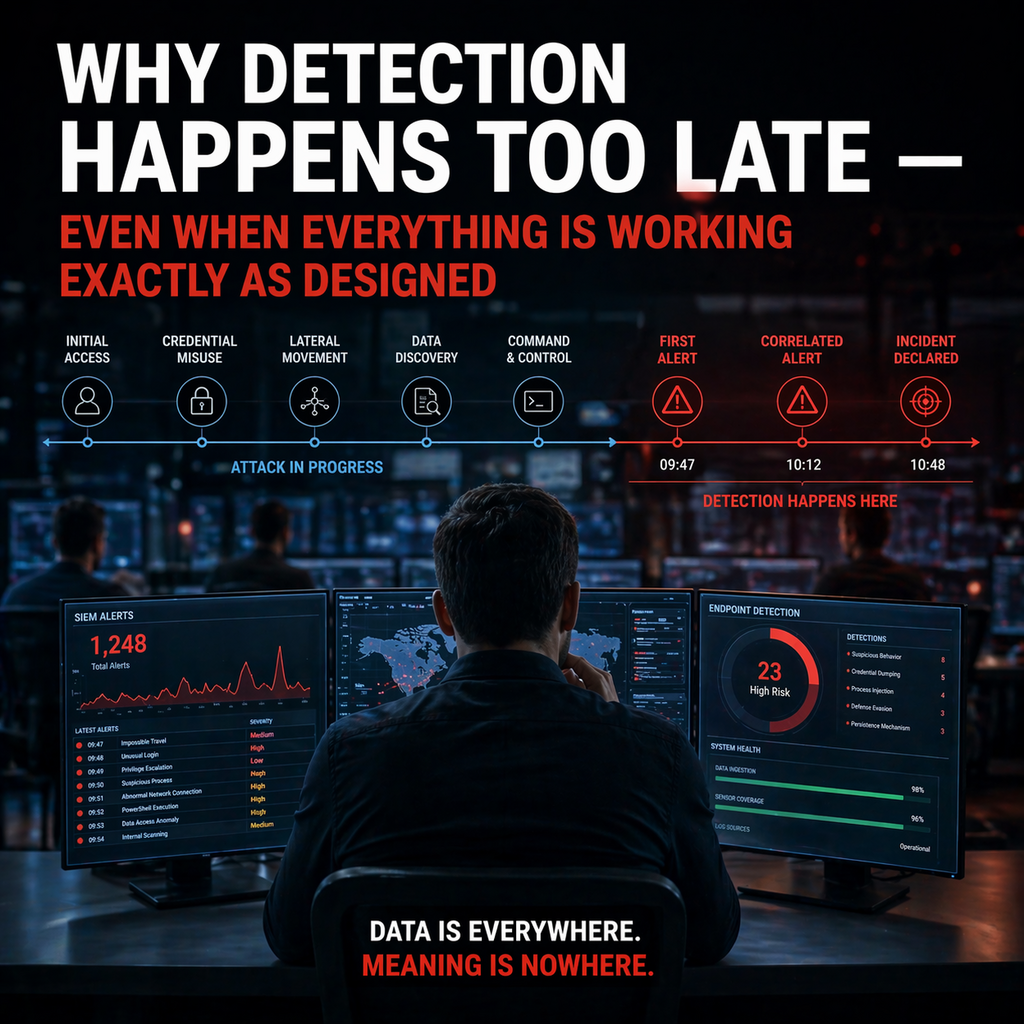
There are few areas in cybersecurity that create as strong an illusion of control as detection. On paper, everything works. Systems are running, data is being collected, alerts are being generated, dashboards are active. The infrastructure is in place, processes are defined, responsibilities are assigned. If you look at these elements individually, the conclusion seems […]
